Prerequisited
Before we start anything, we need two downloads:
Java SE Development Kit
This one is prerequisite for everything else. Just download it, run it and go wild on “Next”. Installation is as easy as it can be.
Installing Eclipse
Installing Eclipse is as easy as unpacking it. For purpose of this walk-through I will unpack it to root directory of drive D: (eclipse.exe will be located in directory D:\eclipse).
Installing Android SDK
Unpack archive to (D:\eclipse) and run “SDK setup.exe” (from “D:\eclipse\android-sdk-windows\SDK setup.exe”). Location is not set in stone but I like it in subdirectory of eclipse. If you desire some other location, just go for it.
As soon as you start it, it will attempt to download newest repository data. If you are behind proxy, this step will fail. In that case just go to “Settings” and fill proxy server and port fields. Often it is also necessary to check “Force https://… sources to be fetched using http://” for everything to download properly.
Once update is completed, you should get list of packages to install. I just leave it at default, check “Accept All”, and click on “Install”. Brace for lengthy download (around 800 MB for Android 2.2).
ADT Plugin for Eclipse
Once you start Eclipse go to “Help”, “Install new software”. Click “Add” once window opens. Now write “ADT Plugin for Eclipse” under site name (exact naming is not important) and “https://dl-ssl.google.com/android/eclipse/” under location. If your Internet access goes over proxy, you will need to use http location “http://dl.google.com/android/eclipse/”.
When packets are found (“Android DDMS” and “Android Development Tools”) I just select them both and click on “Next”/“I accept …”/“Finish” combo few times and download will start. After restart you need to go to “Window”, “Preferences”. There, under “Android” node, you need to select folder with unpacked Android SDK (in my case “D:\eclipse\android-sdk-windows”). All other things I left as default.
After one more restart (I am not really sure it is necessary) you will be able to create new project under “File”,“New”,“Project”:“Android\Android Project”.
Anything more
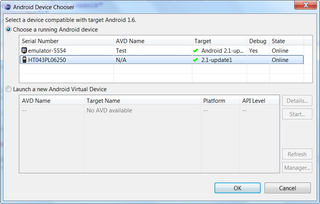
As you attempt to start project, you will get prompt to create emulator. If you would like audience as broad as possible, Android 1.6 is reasonable choice. If you want to target only newer devices, 2.1 is one that you should do your testing on. Those are only rule-of-thumb advices - do not take them too seriously.
If you intend to use command-line tools it would be good to add Android SDK tools to path (for me it is under “D:\eclipse\android-sdk-windows\tools”).
It is definitely not as easy as installing Windows Phone Developer Tools but it is not too bad.